Compliance Confidence
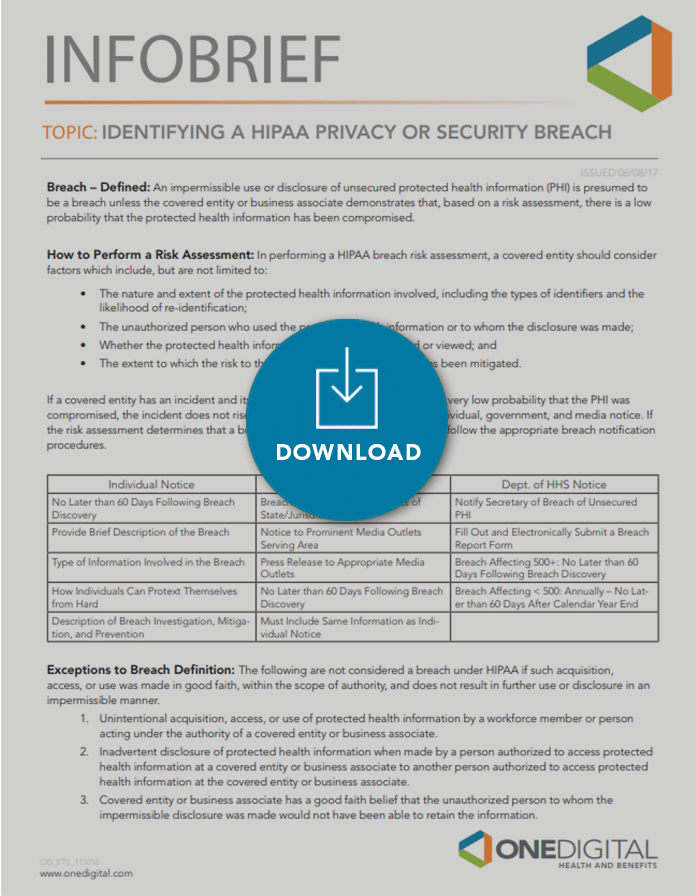
Identifying a HIPAA Privacy or Security Breach
Identifying a HIPAA Privacy or Security Breach
Determine how to identify a HIPAA privacy or security breach and what you need to know about performing a risk assessment.
Understanding your obligations as a group health plan to comply with HIPAA can be challenging, but if your organization possesses protected health information (PHI) being compliant is essential. Know how to conduct a risk assessment so you can discern the probability of compromised PHI and determine how best to proceed to meet your regulatory responsibilities.
DOWNLOAD THE INFOBRIEF: Identifying a HIPAA Privacy or Security Breach
Contact your OneDigital representative for questions and to learn more about best practices regarding HIPAA Privacy and Security or visit our Compliance Confidence page for more information.